There are Numerous softwares available that exclusively deal with Autorun.inf and other Autorun viruses, for example ‘USB Disk Security‘. But Inspite of installing such kind of software, Sometimes you might accidentally open your USB disk Drive (Pen-drive) without looking at the warning by your Antivirus Software and thus Affecting your System with Autorun.inf virus. Once Autorun.inf gets control on your System, it will repeatedly Block any USB Scanning Software preventing it from deleting. It also Restricts you from opening hard drives on a double click.
In such cases, the Traditional Method of deleting Suspicious Programs Using Command Prompt is quite Useful. So Lets start with the Steps:
# 1. Open command prompt. Go to start > Run, and type “cmd” . Press enter.
# 2. Type “cd\” and press enter to get to the root directory of your System.
# 3. Type “attrib -h -r -s autorun.inf” and press enter. This will look for autorun.inf in the selected Drive.
# 4. Type “del autorun.inf” and press enter. This will delete autorun.inf virus from the selected Drive.
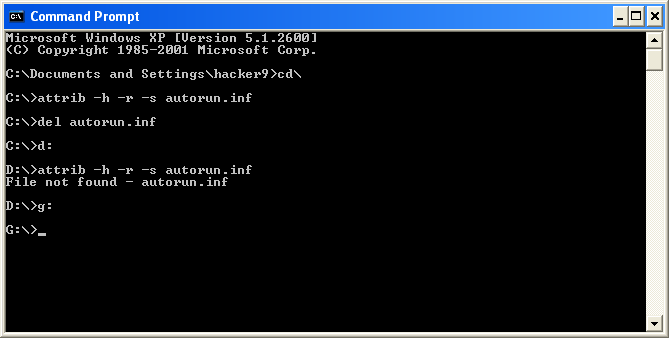
# 5. Repeat the above Steps for other drives. To navigate to other Drives, First type “cls” to clear your ‘command prompt’ then type “d:” . Repeat the Steps for all the Drives including your USB Disk Drive.
# 6. Restart your System.
Delete Autorun.inf Virus without any Software!
Posted by -=[./GENETIK]=- at Wednesday, August 03, 2011 0 comments
Labels: Software
How to hack Facebook via facebook phisher pack
Download Facebook phisher pack by hottechtips.co.cc
Password hottechtips.co.cc
2) Signup for a free webhosting account at 110mb.com, awardspace, or ripway.com
3) Upload all files in your webhosting account
4) suppose your webhosting account is facebooksecurity.110mb/ripway/awardspace.com
5) Final step. Go to http://dot.tk/
6) Rename your facebooksecurity.110mb/ripway/awardspace.com to facebook-security.tk or whatever you want remember start with facebook.tk
7) Passwords will be stored in passwords.txt file
8) Now let the victim login through this link he is trapped and his password is with you
9) Remember not to use this trick on someone who already knows phishing
10) I suggest you to use ripway.com as a free webhosting account as it does not need you to confirm your email address
Try this type of hacking technique mostly on girls
Additionally you can go to any fake sending email and send a fake email to your victim whom you want to hack
Remember before sending fake email you better test a fake email on your id to confirm how email works
Posted by -=[./GENETIK]=- at Wednesday, August 03, 2011 0 comments
Labels: Hacking
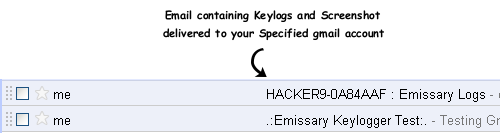
Hacking Facebook Account Password using Free Emissary Keylogger
Not all hacking softwares and keyloggers are Anti-Spywares Shielded. Most Antivirus Softwares are familiar with these free keyloggers and they might flag this keylogger as a Virus. So to experience this keylogger you might need to temporarily turn off your antivirus or uninstall it. But Don’t worry, if your victims antivirus is not up to date or freeone, there are high chances that you may end up getting his keylogs. So give it a Try.
 -Features of Emissary Keylogger:
-Features of Emissary Keylogger:
- Can mail all the Keystrokes including login details
- Can send screenshots of the victim’s Screen
- Can Block VirusScanning Websites on victim’s computer
- Can Disable TaskManager on victim’s PC
- Can Disable Regedit on victim’s PC
 -How to Use this Keylogger to hack Facebook Password?
-How to Use this Keylogger to hack Facebook Password?
First make sure you have ‘Microsoft’s .net Framework‘ installed on your PC, if you dont have please download and install it. [*] The victim need not have .net framework. Follow the Steps below:Step 1: Download ‘Emissary Keylogger‘ Software and extract the files to desktop. If your Antivirus deletes the file, then please turnoff your Antivirus or uninstall it and try downloading again.
Step 2: Run ‘Emissary.exe’ file and enter your gmail account details, so that the password and other info of your victim can be mailed to you. If you are afraid of entering your gmail details, then do create one temporary fake account and enter those details.
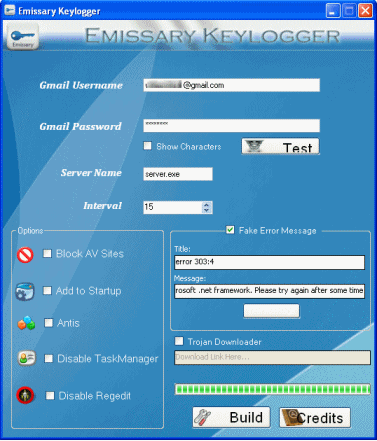
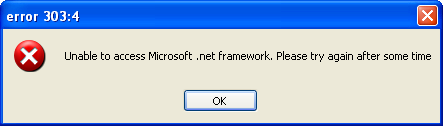
Step 3: After you enter your ‘Gmail account’ details Click on ‘Test’ to test the connection to your Gmail account. In the Server name Field you can change the name if you want. enter any Time Interval in the interval field. This timer controls the time interval between two keylogs emails. You can also show fake error message to your Victim when he clicks your server.exe file. to do so enter the error title and description in the ‘Fake error message’ field.
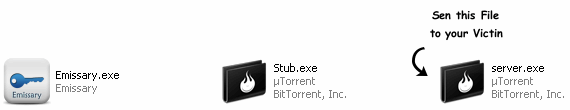
Step4: Now after filling the required fields, Click ‘Build’ button. This will create another file called server.exe in the same directory.
Step5: Now send this server.exe file to victim and make him install it on his computer. You can use Binder or Crypter to bind this server.exe file with say any .mp3 file so that whenever victim runs mp3 file, server is automatically installed on his computer without his knowledge. also read: How to change ICON of .exe file?
[ * ] Now because this is a free keylogger, you can’t send server.exe file via email. Almost all email domains have security policy which does not allow sending .exe files. So to do this you need to compress the file with WinRar or upload it to Free File Storage Domains, like Mediafire, rapidshare, filethief etc.
Step6: Once the victim runs your sent keylogger file on his computer, it searches for all the stored usernames and passwords and it will send you email containing all keylogs and screenshots regularly after the specified ‘Time interval’.
Posted by -=[./GENETIK]=- at Wednesday, August 03, 2011 1 comments
Labels: Hacking
How to Control a Remote Computer using Lost Door

Remote Administration tools also known as RAT are windows Trojans or in simple terms programs used by a Hacker to get administrative privileges on the victim’s computer. Using a RAT you can do a lot of cool things such as “Upload, delete or modify data” , “Edit registry”, “Capture victim’s screen shot”, “Take control of victim’s Computer”or “Execute a virus” just with a click of a button.
Throughout this article I will teach you how to use Lost Door, a Windows RAT, to control and monitor a victim’s computer remotely.
Disclaimer: Coder and related sites are not responsible for any abuse done using this software.
Follow the steps below to setup a server for Lost Door.
- Download Lost Door from here . (Update: In case the given download link doesn’t work, use this secondary download link. The password to unzip this file is “ehacking.nethungry-hacker.com” without double quotes.)
- On executing the download file, you will see the following screen. Accept it
- After it is open, right click on the window and click on create server
- Now enter your IP address and DNS here. Leave the rest of the field as it is.
- Now click on the ‘Options’ tab and choose the options as you want. To activate an offline keylogger is a good practice.
- Now go to ‘Advanced’ Tab. There will options related to spreading. This will be used in case you have more than 1 victim.
- Now just go to the ‘Create’ tab and click on create server. Your server is ready for use now and now send it to the victim.
Sending the server file to your victim
- If you have physical access to the victim’s computer then take the server file in a pen drive and just double click on your server file once you have injected the pen drive into that computer.
- For those who don’t have physical access can use social engineering in order to get the victim execute that file on his computer.
Using Spreading to affect multiple victims
Posted by -=[./GENETIK]=- at Wednesday, August 03, 2011 0 comments
Labels: Hacking
How To Hack Your School Network
This tutorial is for those newbies out there, wanting to "hack" their school. I'm gonna start by saying, if your going to hack the school, theres a high probability your get caught, and don't do anything dumb like deleting the network. Its lame, and you will get flamed for doing it. This hack will allow you to take control of the PC's at school. Lets start:
How to take control of the PC's at school:
Here are the steps;
- Preparing The Virus
- Setting Up The Virus
- Controlling The PC
Obviously, if you gonna take control over your school PC you need a virus. You have 2 methods:
- The virus I made which is harmless and you won't even notice it was executed.
- Dropping a Trojan on the school PC.
What you need:
- Pen Drive (You can buy one, or you just use yours)
- Brain (You can't buy this)
Now, open notepad and copy/paste this code: the code
Save the file as something.bat (you can change something to whatever you want). In "Save as type:" choose "All Files".

I strongly recommend you not to change the rdport and tnport configuration. The rdport will open the remote desktop default port, and the tnport will open the telnet's client default port.
You can change the username, password and the rport (randomn port you choose to be opened)
At ipconfig /all >> C:\attach.txt you must change C:/ by your pen drive letter.
Save it and remove your pen drive.
Take your pen drive to school and run the bat file. Don't forget the pc you runned it in cause you might need it.
When you get home go to your pc and try to telnet them or remote desktop the PC.
Method 2:
In this method we will use a Trojan to control the school PC.
Here is a tutorial about how to create a Trojan: ProRat Trojan
Now just create a server (there is an explanation in the tutorial above), bind it and put it into your pen drive. Make sure you leave your PC turned on.
Then go to your school and drop the trojan.
Other way to do this is to give your trojan to a friend and tell him to stay in school. When you arrive home, send him a SMS and tell him to drop the trojan. This way you could even see if it worked.
After this you can probably do whatever you want with the PC.
Posted by -=[./GENETIK]=- at Wednesday, August 03, 2011 0 comments
Labels: Hacking
How to Hack E-Mail Account Password - Email Hacking Software
Now you know that there are many ways to hack email password, like bruteforcing, social engineering or Reverting, but the main two methods used to hack email passwords are Remote Keylogging and Phishing. In this article i'll show you how to hack email account password using keyloggers and trojans. Here I am demonstrating using PRORAT trojan. You can use any trojan or keylogger as per your ease. The basic functionality of all backdoors are same. Pls make note that all these hacking tools and softwares are detected by antivirus. You have to uninstall or close you running antivirus first. Now we can start.
How to Hack Email Account Passwords Using ProRat?
1. First of all Download ProRat. Once it is downloaded right click on the folder and choose to extract it. A password prompt will come up. The password will be "pro".
2. Open up the program. You should see the following:

3. Next we will create the ProRat Trojan server. Click on the "Create" button in the bottom. Choose "Create ProRat Server".

4. Next put in your IP address so the server could connect to you. If you don’t know your IP address click on the little arrow to have it filled in for you automatically. Next put in your e-mail so that when and if a victim gets infected it will send you a message. We will not be using the rest of the options.

5. Now Open General settings. This tab is the most important tab. In the check boxes, we will choose the server port the program will connect through, the password you will be asked to enter when the victim is infected and you wish to connect with them, and the victim name. As you can see ProRat has the ability to disable the windows firewall and hide itself from being displayed in the task manager.
Here is a quick overview of what they mean and which should be checked:

6. Click on the Bind with File button to continue. Here you will have the option to bind the trojan server file with another file. Remember a trojan can only be executed if a human runs it. So by binding it with a legitimate file like a text document or a game, the chances of someone clicking it go up. Check the bind option and select a file to bind it to. A good suggestion is a picture or an ordinary text document because that is a small file and its easier to send to the people you need.

7. Click on the Server Extensions button to continue. Here you choose what kind of server file to generate. I prefer using .exe files, because it is cryptable and has icon support, but exe’s looks suspicious so it would be smart to change it.

8. Click on Server Icon to continue. Here you will choose an icon for your server file to have. The icons help mask what the file actually is. For my example I will choose the regular text document icon since my file is a text document.
 9. After this, press Create server, your server will be in the same folder as ProRat. A new file with name "binded_server" will be created. Rename this file to something describing the picture. A hacker could also put it up as a torrent pretending it is something else, like the latest game that just came out so he could get people to download it.
9. After this, press Create server, your server will be in the same folder as ProRat. A new file with name "binded_server" will be created. Rename this file to something describing the picture. A hacker could also put it up as a torrent pretending it is something else, like the latest game that just came out so he could get people to download it.
Very important: Do not open the "binded_server" file on your system.
10. You can send this trojan server via email, pendrive or if you have physical access to the system, go and run the file. You can not send this file via email as "server.exe", because it will be detected as trojan or virus. Password protect this file with ZIP and then email it. Once your victim download this ZIP file, ask him to unlock it using ZIP password. When the victim will double click on the file, he will be in your control.
11. Now, I will show you what happens when a victim installs the server onto his computer and what the hacker could do next.
Once the victim runs the server on his computer, the trojan will be installed onto his computer in the background. The hacker would then get a message telling him that the victim was infected. He would then connect to his computer by typing in his IP address, port and clicking Connect. He will be asked for the password that he made when he created the server. Once he types it in, he will be connected to the victims computer and have full control over it.

12. Now the hacker has a lot of options to choose from as you can see on the right. He has access to all victim's computer files, he can shut down his pc, get all the saved passwords off his computer, send a message to his computer, format his whole hard drive, take a screen shot of his computer, and so much more. Below I’ll show you a few examples.

13. The image below shows the message that the victim would get on his screen if the hacker chose to message him.

14. Below is an image of the victims task bar after the hacker clicks on Hide Start Button.

15. Below is an image of what the hacker would see if he chose to take a screen shot of the victims screen.

As you saw in the above example, a hacker can do a lot of silly things or a lot of damage to the victim. ProRat is a very well known trojan so if the victim has an anti-virus program installed he most likely won’t get infected. Many skilled hackers can program their own viruses and Trojans that can easily bypass anti-virus programs.
Posted by -=[./GENETIK]=- at Wednesday, August 03, 2011 0 comments
Labels: Hacking
Visual Basic Undetecting Tool to Hide Trojans, RATs and Keyloggers from Antivirus Softwares
In this article i'll show you a Visual Basic Undetecting Tool to hide our viruses, keyloggers or any RAT tool from antiviruses so that they are not detected and deleted by antiviruses. This amazing tool does FUD a source making a new stub and FUD with no dependencies on others every time you want it.

VB Undetecting Tool Features:
- You can select with which files you want to work.
- It works totally automatically.
- You do not need to have Visual Basic Installed as it has a Compiler.
- It works very fasts and complexes all code in less than 1 minute (Depending code long)
- It FUDS Your tools and protects it against crackers, As new generated code is totally unreadeable by debuggers
- New generated codes are totally different between them, no one is similar to other, they are all UNIQUE.
- If an AV gets one code you undetected with this tool, the others continue being undetected as they are UNIQUE.
- It has a Plug-ins Folder, so, you can code your own tools for the program and personalizate it.
- Tool will never be out of date as it is continually being updated, and if it does, however, you can code your own trashs simplily.
- Api Obfuscating: It obfuscates API'S, and also names!!
- String Encrypting: It encrypts ALL String with RANDOM key, they will be every time different.
- Add XOR Function: It adds automatically the Decryption Function
- Add Trash Code: It adds Trash Code, which you can code using plug-in folders or use default one.
- Complex Code: It does RIP on code, I mean, It changes code order and redirects the coding, making it continuing working and redirectioning flows.
- Trash Modules, Forms And Classes: It adds random new modules, Forms or Classes.
- Trash Declarations: It adds Trash Main Declarations, which you can code new ones with plug-ins folder.
- Trash Functions: It adds Trash Functions to project, which you can code new ones with plug-in folder.
- Trash Functions Options: It adds new options to the existing functions.
- Randomize Function Names: It changes all Function Names to randomized strings.
- Randomize Subs Names: It changes all Subs Names to randomized strings.
- Randomize Project Info: It changes all Project Info to randomized strings.
- Randomize Objects Names: It changes all module, forms and classes names to randomized strings.
- Scramble Function Orders: It changes the order of the functions appearing in each module,form or class to randomized order.
- Scramble Main Declarations: It changes the order of the main declarations appearing in each module, form or class to randomized order.
- Scramble Sub Declaration Orders: It changes the order of each declaration in each function or sub appearing in each module, form or class to randomized order.
- Don't Check for Repeated Keys: This might bug project, but tool will run faster.
- Use Fast Replace: This rarely will bug project, but tool will run faster.
- Don't Work with new Objects: This options disables working with the new trash modules, forms or classes.
- Disable Random Work: This option will disable Random Work, this will make no important difference in Project.
- Debug Mode: Ballon Showing Tips will inform you program running information when its working.
- Compile: After a new stub has been generated it will automatically Compile It.
- You can do a multi generating of Stubs, so you can use it as Stub Generator.
Download Visual Basic Undetecting Tool
Posted by -=[./GENETIK]=- at Wednesday, August 03, 2011 0 comments
Labels: Hacking
Subscribe yoo :D
| Jam Sekarang |
|
| Tanggal |
|
| Salam Sapa | : |
| Status Admin | : Online* |
| Terjadwal : Berarti yang punya blog tidak bisa berinternet |







